CYBERSECURITY: An Emerging Technology in Business Planning.
In this article we will discuss:
- What is cybersecurity?
- Scale of Cybersecurity
- How to achieve Cybersecurity?
- Importance and benefits of Cybersecurity.
- Types of Cybersecurity
- Classification of Cyber Attacks
- How to implement a Cybersecurity plan?
- Future of Cybersecurity in business
- Common Cybersecurity safety tips
- Skills required to become Cybersecurity professional
Due to the digital transformation of our business process, Cybersecurity technology has become essential for our business. Cloud computing, remote work expansion, AI-powered chatbots, and various digital trends have made information technology and its networks vulnerable to cyberattacks.
Such attacks can steal or destroy sensitive data and extort money from you. It will eventually harm your business and even damage the company’s reputation. After the COVID-19 pandemic, many people are working from home, so it’s become crucial to provide a strong cybersecurity network to our business.
What is Cybersecurity?
Cybersecurity is a complete framework for your business that involves various processes to protect your IT networks and systems, your software and data from any intrusions and other cyberattacks. It is also known as an information security system for computer servers, mobile devices, and electronic systems.
It involves various processes and tools to identify and block such threats. It is run by CISO (Chief information security officer), who leads the cybersecurity team. However, apart from this, the organization should make its employees aware of cybersecurity threats.
Scale of Cybersecurity
An article published in The Hindu Newspaper reveals that this year ‘cyberattacks hit 26,000 Indian Websites in the last ten months.
CERT-In has reported 17,560 websites in 2018 and 24,768 websites in 2019 were hacked by hackers. In the year 2020, 26,121 websites were hacked by cybercriminals, and the numbers increased again in 2021 with the hacking of 25,870 Indian websites till October. The Indian Computer Emergency Response Team (CERT-In) is responsible for tracking and monitoring cybersecurity incidents in India.
The data breaching incidents of Facebook in April 2019 exposed the data of 533 million users worldwide. Another incident of LinkedIn in June 2021 where data of its 700 million users were posted on the dark web, influencing more than 90% of its user base.
The scale of cybersecurity threats will keep rising worldwide. Hence, businesses across the globe should respond to this rising threat and implement valuable cybersecurity measures to combat cyberattacks.
Components of Cybersecurity technology for business:
We have already discussed that flaws in cybersecurity systems can lead to malicious attacks on our sensitive data. Hackers can access and delete our data, extort money and infiltrate our business process. Cybersecurity has three major components:
*Cybersecurity
*Information security
*Network security
- Cybersecurity- Cybersecurity is a subset of IT security. It protects digital data present on your networks, servers, and computers from cyber attacks.
- Information security- Information security software protects the physical and digital data from invaders. It secures information transferred within a network and data stored at the server.
- Network security- Network security uses hardware and software for data protection. It protects data sent from your computer to other network devices. As a whole, it protects the IT infrastructure’s sensitive information from alteration by cybercriminals.
Importance and benefits of Cybersecurity Technology:
The organization can avoid various business issues by developing a Cybersecurity network that will benefit your business in many ways. Your company can run smoothly without any financial loss caused by cyberattacks. You can explain to your board members how security measures have made a significant contribution in running their business flawlessly.
You can list the number of data intrusion attempts on your server and their response recovery time. Later on, you can plan a strategy to defend against such cyberattacks.
Types of Cybersecurity Technology:
There are various types of Cybersecurity Technologies provided for businesses according to their requirements and needs. Let us discuss each of them:
- Network Security: As its name says, it protects your computer networks from intruders and other threats. It provides hardware and software solutions to safeguard them from attackers, a set of rules and configurations to access the network by providing overall protection. It includes Remote Access VPN, firewall and zero-trust network access.
- Application Security: It is a process to make an application more secure by developing, adding and testing the security features of an application. These security features are added during the developmental stage of an application to improve its security.
- Informational Security: It is also known as InfoSec. It has a set of plans designed to protect your data from unauthorized access. It alters your information when you transmit it from one system to another. It protects data from being modified and destroyed.
- Cloud Security: The data stored online over the cloud computing platform is guarded by Cloud Security software to eliminate the risk of attacks. It includes firewall protection, virtual private networks protection. It averts users to use public internet connections.
- Preventing Data Loss: The organization has to develop policies to prevent data loss. They have to make a recovery plan at the back front if a cybersecurity breach occurs. It also includes making plans for data storage and fixing network permission.
- End-user education: A user needs to be informed about best Cybersecurity practices. If an individual accidentally uploads any malware or malicious code to its laptop, it could result in data or financial loss. Users should not click or download any suspicious links and attachments in emails that allow any malware to penetrate your software system.
Classification of cyberattacks:
Cyberthreats are of three categories. They are confidentiality, integrity and availability. It is known as the CIA triad that guides companies and organizations to make their security plans.
- Confidentiality: The information is between you and your clients, such as your bank account or credit card details. They are kept confidential from your co-workers or friends.
- Integrity: Integrity is to safeguard the data stored in your computer. It ensures that given data is true and accurate without any modifications. A cybercriminal tries to leak users’ data from a public platform which influences its users to lose their trust in an organization and damage its reputation.
- Availability: If a user’s sensitive information is accessible by a cybercriminal, he will block that information accessed by its user. In exchange, he will demand a ransom to pay only then the user can have access to its data.
Threats on Cybersecurity:
Cyberattacks can disrupt the image of an organization and create a mess in their business. Common cyber attacks are malware, ransomware, man-in-middle, or phishing within your network.
- Malware: It is malicious software that enters a user’s computer. It enters the system by clicking on an unknown email attachment or any genuine-looking download link. It is used by criminals to earn money online or disrupt the computer system of the user. Malwares are of different types:
- Virus
- Trojans
- Ransomware
- Spyware
- Botnets: It is a network of computers that are affected due to malware attacks. The hackers use it remotely to do email spamming and other online frauds.
- SQL injection: An SQL (structured language query) injection attack is on your database. Cybercriminals take control of the database and steal information from it. They take advantage of such applications that are vulnerable to cyberattacks and insert malicious code through SQL statements. It allows them to access sensitive information.
- Phishing: A Phishing attack is made by duping people and requesting to give their personal information like credit card details. A user is targeted by email, sent by a genuine company, asking for the user’s personal information.
- Man-in-the-middle attack: A cybercriminal intercepts the data over an insecure Wi-Fi network. It steals the data sent between the user and its network.
- Denial-of-service attack: Cybercriminals will prevent an organization from sending requests or data operations. They do it by falsely increasing the traffic within the network.
- Distributed Denial of Service (DDoS): The targeted website is attacked by sending multiple requests which surpass the website’s capacity to handle these requests. Hence, prevent the website from running smoothly.
How to implement a cybersecurity plan?
Every organization working in cyberspace should make a cybersecurity plan to protect their user’s data and sensitive information vulnerable to cyber attackers.
- Determine the cyber threat level: Analyze the kinds of cyber threats your organization is suffering. Find up to which level such attacks can harm your business.
- Access your cyber security framework: Access the current cybersecurity framework of your organization for all categories that are policies, threat recovery plans and security technologies.
- Identify the cybersecurity flaws and improve them: Look for the modification points in the current framework. You can check the pros and cons of each modification. In the end, you can give your presentation to the upper management for review.
- Document your final plan: Document all your procedures and guidelines and assign responsibility to each person who carries out the cybersecurity operations. Finally, update your team by providing training or initiating any cybersecurity awareness week.
Future of Cybersecurity in business:
Soon people will prefer to work remotely. This trend has started slowly after the COVID-19 pandemic. There has been a significant increase in remote working. Now, this again poses a cybersecurity threat for people who are working from home. In the future, what changes an organization can make to improve its Cybersecurity technology:
- Escalate security automation: Cyber attackers are using AI and machine learning to infiltrate within our secure network, in the same way, we can also use AI tools to manage and fix it at the beginning. AI tools can even identify malicious code that a user can not notice.
- Adopt zero trust security: It works on a principle that no device is trustworthy before its verification. Adopting a zero-trust approach for security can reduce the frequency of cyberattacks.
- Improve threat response capacities: Every organization should have a backup plan in case an incident of data breach or ransomware occurs. Make strategy ready to use, so there will be less impact on working.
- Find out the source or chain of threats: Ask your cybersecurity expert to look deep and find the source. It can be a known person within your organization. It can be your business rival who is making targeted attacks on your business to demolish your image among your clients.
Common cybersecurity safety tips:
An Individual or a business organization can shield themselves by following these cyber safety tips:
@Always update your system’s software: It will save your system from the latest threats and keep malwares attacks at bay.
@ Install anti-virus software on computer: Anti-virus software will not allow any suspicious code to enter your system and give a warning if you click on any unknown link.
@ Use high-security password: Use an alphanumeric password to protect your data.
@ Never open unknown email attachment: Such attachment has malicious code that will copy your data or modify it. They can hack your computer and ask for ransom.
@ Never use public WiFi network: Using unsecured Wifi networks will leave the system vulnerable to cyber threats.
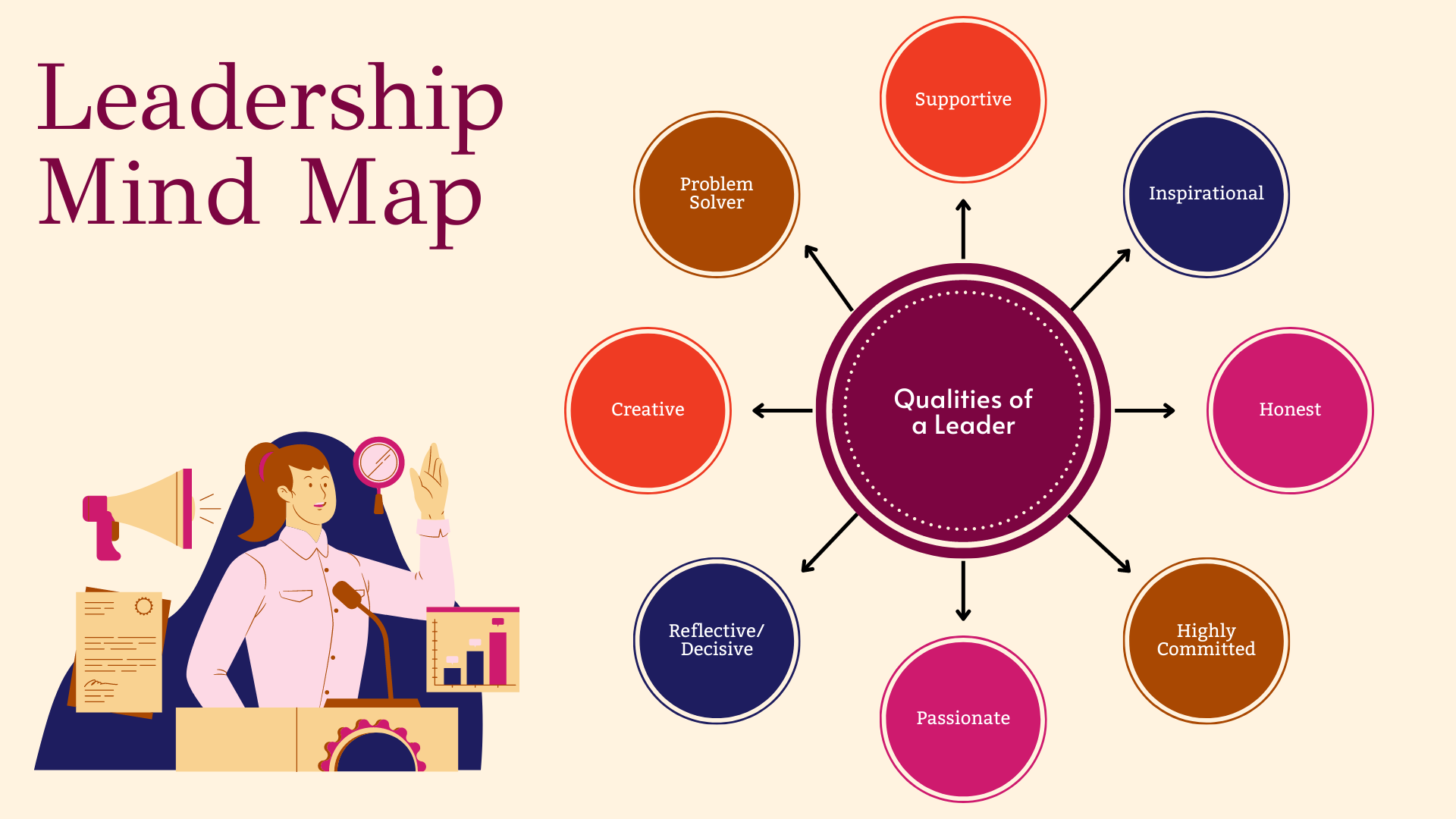
Skills required to become a Cybersecurity professional.
Due to increasing cyber threats, online businesses are spending on cybersecurity infrastructure resulting in high demand for a skilled cybersecurity workforce. According to The US Bureau of Labor Statistics’ Information Security Analyst’s Outlook, cybersecurity jobs are among the fastest-growing careers. It predicts cybersecurity jobs will grow 31% through 2029.
- In the coming future, there will be plenty of job opportunities in this domain. Let’s check the skills required for this career to enter into it.
- Application security development
- Cloud security
- Threat intelligence analysis
- Penetration testing/red teaming
- Network security
- Identify and access management
- Risk and compliance auditing
- Mobile remote computing
Working professionals and college graduates can explore job opportunities in cybersecurity after completing an online course. They will learn these skills to reinforce their knowledge in this emerging field.
How useful was this post?
Click on a star to rate it!
Average rating 5 / 5. Vote count: 5
No votes so far! Be the first to rate this post.